Simplify bare metal operations for sovereign clouds
David Beamonte
on 30 March 2026
The way enterprises are thinking about their infrastructure has changed.
Digital sovereignty of all kinds – data sovereignty, operational sovereignty, and software sovereignty – have begun to dominate the infrastructure discussion. Today, these abstract terms have become practical concerns for platform teams. Changing regulations, geopolitical uncertainty, and growing concerns about vendor dependency are forcing organizations to take a closer look at where their infrastructure runs, and who truly controls it.
We’ve discussed how to achieve enhanced data security in your sovereign cloud previously. However, in this blog, we’ll be diving into an underexplored topic: the metal underlying sovereign clouds. We’ll consider sovereignty and how it relates to infrastructure, highlighting the reasons why avoiding vendor dependence is so important, and how bare metal automation can help to make sovereignty sustainable.
Sovereignty: getting control of your metal
Most enterprises aiming to improve their control over their data and infrastructure begin with data sovereignty. Data residency, encryption, access controls, and compliance frameworks are the most visible requirements, and they are usually the first to be addressed. These measures are necessary, but they only answer part of the question. For a deep dive into the factors driving sovereignty, and why data sovereignty isn’t enough, check out our webpage and our whitepaper, “Sovereign cloud: the essential guide for enterprises.”
For sovereign clouds, a specific aspect is often overlooked: the ability to provision, change, and recover infrastructure independently, without relying on vendor-specific tooling. Control on paper does not always translate into control in practice, especially below the operating system.

Operational dependency is a sovereignty risk
The weakest point in many sovereign cloud designs lives beneath the layers that platform teams usually focus on. Firmware, bootloaders, out-of-band management interfaces, and provisioning workflows are frequently invisible to application teams, and often poorly documented.
Having control over your infrastructure is not limited to where your hardware is located, or who owns it; it’s also crucial to consider how it is operated. When those processes depend on proprietary tools, vendor-specific interfaces, or undocumented workflows, the operational dependency becomes a real risk.
These dependencies are often invisible until something changes: a vendor contract ends, hardware needs to be upgraded to newer or more capable machines, or key platform engineers leave the organization. Suddenly, the ability to operate the infrastructure independently disappears.
Several common risks show up at the bare metal layer. Firstly, you cannot audit what you do not control. When provisioning is manual or handled by third parties, it becomes difficult to maintain a clear view of what is actually running on each server. Firmware versions, boot settings, network configuration, and management interfaces differ from machine to machine and are outside the scope of most platforms.
Secondly, having unclear foundations makes it harder to manage what is built on top. The reliability of encryption, access policies, and application security relies on a stable and predictable inventory and provisioning process. Because of this, operational dependency becomes a structural risk. Manual workflows, proprietary provisioning tools, or knowledge concentrated in a small team create hidden dependencies that don’t scale well.
Finally, slow provisioning makes it harder to maintain sovereignty over time. Sovereign platforms need to scale, recover, and evolve. When bringing new hardware online takes too long or requires manual coordination, maintaining control becomes harder with every change.
When building your sovereign cloud, it is important to avoid these traps. A sovereign platform must be something the organization can operate, evolve, and recover on its own terms, even as people, vendors, and hardware change.
Bare metal automation makes sovereignty sustainable
Bare metal automation addresses these risks by bringing consistency to the lowest layer of the stack. Instead of treating physical servers as special cases, it treats them as flexible programmable assets, establishing the same processes from virtual machines to bare metal.
In particular, bare metal automation provides several specific capabilities that matter for sovereign clouds:
- Transparent hardware inventory: Servers and their internal hardware capabilities are discovered, inventoried and commissioned, providing a single source of truth. This is essential when infrastructure ownership and configuration must be demonstrable to regulators and auditors, supporting robust compliance within a sovereign cloud.
- Repeatable provisioning: Servers are provisioned the same way every time, using defined and versioned processes. This makes the infrastructure easier to rebuild when sovereignty depends on reproducibility instead of trust.
- Clear ownership of the provisioning pipeline: The organization controls how machines are discovered, configured, and brought into service, without relying on vendor-specific tooling or external actors, preserving operational control over the physical layer.
- Faster, more reliable operations: New hardware can be added, replaced, or repurposed quickly, allowing sovereign platforms to scale, recover, and evolve without losing control during routine changes or exceptional events..
- Hardware testing before and after production: Hardware needs to be tested before going into production, helping ensure that only known, compliant machines are part of the sovereign infrastructure.
- Less dependence on tribal knowledge: Operational knowledge is captured in systems and processes rather than living only in people’s heads, reducing the risk that sovereignty depends on specific individuals rather than the organisation itself.
Together, these capabilities turn sovereignty into something that can be maintained over time. Control of the physical layer becomes explicit, verifiable, and repeatable, which is exactly what sovereign cloud initiatives depend on as they move from initial deployment to long-term operation.
Closing the gap with MAAS
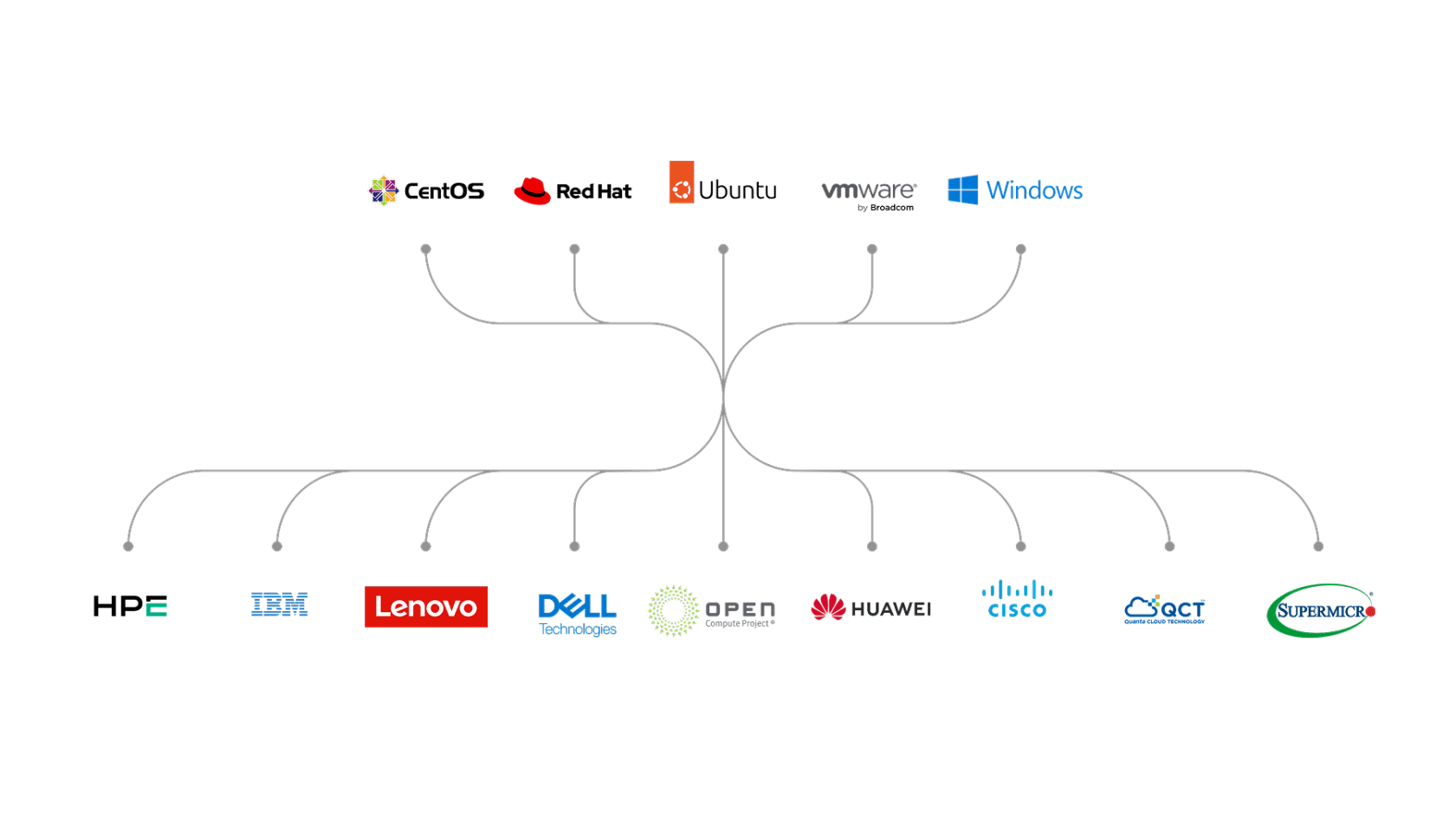
Bare metal automation platforms exist to address this exact problem. Canonical MAAS is an open source platform that provides a central control plane for managing and provisioning physical servers using infrastructure-as-code principles. It offers a consistent, cloud-like management experience for pools of physical servers across heterogeneous hardware environments, making it easier for platform teams to apply the same operational practices everywhere.
Several aspects of MAAS are particularly relevant in the sovereign cloud context. Together, they address the need for demonstrable control, operational independence, and repeatability at the physical layer, which are crucial for sovereign cloud initiatives:
- End-to-end lifecycle control: MAAS automates the full lifecycle of physical machines, from discovery and commissioning to deployment, reuse, and decommissioning. Using standard out-of-band management interfaces such as IPMI or RedFish, it keeps power control and provisioning across a wide range of certified hardware without the need of vendor-specific tooling.
- Infrastructure as code for bare metal: A stable, well-defined API allows hardware to be managed programmatically and integrated into existing workflows. Treating physical infrastructure as code makes provisioning repeatable, auditable, and easier to evolve without relying on manual intervention.
- Hardware validation at scale: Built-in diagnostics allow machines to be tested before they enter production and again when they are recycled or repurposed. This helps maintain a healthy and compliant pool of servers, which is essential for predictable operations and reliable recovery.
- Accurate inventory and configuration awareness: Detailed hardware inventory makes it possible to place workloads based on real capabilities.
- Integrated network configuration and services: MAAS configures server network interfaces with bridges, VLANs, bonds and addresses, and it integrates highly available, open source DHCP and DNS services.
Taken together, these capabilities address the gaps that often undermine sovereign cloud efforts at the physical layer, and they give platform teams a way to operate bare metal with the same level of control, visibility, and discipline they expect from higher layers of the stack.
Conclusions and next steps
Sovereign clouds only work if control can be maintained over time. Data protection and application-level controls are important, but they depend on how the infrastructure underneath is built and operated. When the physical layer is opaque or hard to manage, sovereignty is difficult to implement.
Bare metal management is where many of these issues surface. Automating this layer reduces the dependency on vendors and individuals, makes infrastructure easier to audit, and allows platforms to evolve without losing control.
For organizations serious about sovereign infrastructure, this is not about adding another tool. The core idea is to establish the foundational layer in a way that sustains long-term sovereignty.
MAAS is designed to help teams bring that level of control to physical infrastructure. If you are thinking about your cloud sovereignty strategy and rethinking how you run bare metal today, it is worth taking the time to see how MAAS works and what problems it can remove from daily operations.
You can try MAAS on your own and decide whether it fits your platform. If you want help designing or running MAAS at scale, Canonical also provides professional support. Reach out if you would like to discuss your requirements or take the next step.
Talk to us today
Interested in running Ubuntu in your organisation?
Newsletter signup
Related posts
How to Harden Ubuntu SSH: From static keys to cloud identity
30 years after its introduction, Secure Shell (SSH) remains the ubiquitous gateway for administration, making it a primary target for brute force attacks and...
The “scanner report has to be green” trap
Stability, backports, and hidden risks of the bleeding edge In the modern DevSecOps world, CISOs are constantly looking for signals in the noise, and the...
Modern Linux identity management: from local auth to the cloud with Ubuntu
The modern enterprise operates in a hybrid world where on-premises infrastructure coexists with cloud services, and security threats evolve daily. IT...
